虽然许多人每天可能会使用蓝牙,但大多数人不知道蓝牙的工作原理或会被黑客入侵。蓝牙黑客攻击为进入目标世界提供了清晰的窗口。几乎每个设备都具有蓝牙功能,人们在手机和平板电脑上存储了大量个人信息。破解他们的蓝牙连接,您也许可以访问所有这些数据。
【linux网卡蓝牙适配器专卖店:https://shop307204092.taobao.com】
尽管蓝牙与Wi-Fi共享相同的2.4 GHz频率,但由于协议不完全相同,因此属性有所不同。安全性得到了增强,因此流行的Wi-Fi黑客工具无法在蓝牙上运行。
一方面,它们一直在跳频,因此,如果您有两个通过蓝牙通信的设备,它们都使用每秒将频率偏移多次的算法。这意味着我们不能只坐在一个频率上聆听,因为它们将在各处跳跃。首先,它使攻击者很难收听对话。
不要错过:机器人先生如何破解蓝牙
另一个特性是,蓝牙不会像Wi-Fi那样每次都协商密钥,任何人都可以轻松地加入和退出Wi-Fi网络。取而代之的是,蓝牙一开始会协商一次密钥,存储密钥,然后在每次看到同一设备时都对其进行引用。这意味着不可能坐在那里嗅探钥匙,因为您需要在这些设备第一次通信时就在那里。否则,您将无法获得任何有用的信息,并且不可能像使用Wi-Fi一样跳入对话。
但是,我们仍然可以跟踪附近的蓝牙设备,从中读取信息,甚至可以写出特定的特征。因此,进行侦查很有用,以防我们可以控制设备,识别漏洞或以后找到与附近漏洞匹配的漏洞。
蓝牙侦探需要什么
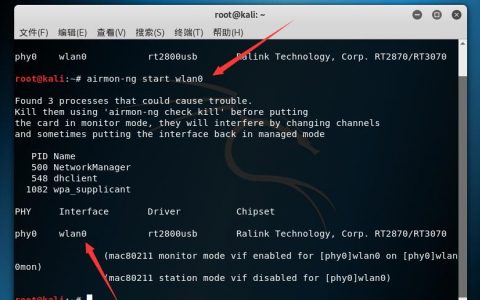
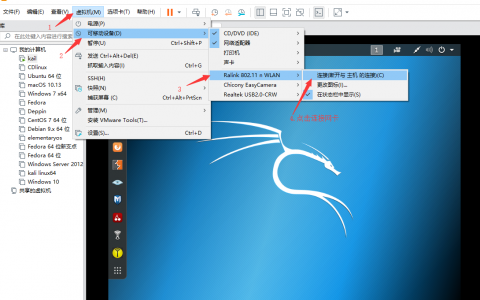
要开始蓝牙监视,您将需要安装Kali Linux的完整更新版本,因为我们将使用内置的蓝牙工具。为了使事情变得最基础,我们没有安装任何额外的东西,我们可以使用默认情况下Kali Linux拥有的蓝牙工具。
我们将在下面介绍的内置工具包括hciconfig,hcitool,sdptool,l2ping和btscanner。这些工具中的许多工具都包含在BlueZ中,BlueZ是几乎每个版本的Linux(包括Kali)中的默认蓝牙协议堆栈。(我们还将在Kali中使用一些专用工具进行蓝牙侦察。)
当然,我们必须非常接近破解蓝牙。借助出色的蓝牙适配器,您应该能够在咖啡店,学校教室,办公室甚至邻居家中使用蓝牙设备。
不要错过:使用MultiBlue通过蓝牙控制任何移动设备
步骤1使用hciconfig启用蓝牙适配器
如果您熟悉用于Wi-Fi卡和适配器的ifconfig,那么还有另一个与蓝牙设备相似的工具。它称为hciconfig。
~# hciconfig
hci0 Type: Primary Bus: USB
BD Address: ██:██:██:██:██:██ ACL MTU: 1022:8 SCO MTU: 183.5
DOWN
RX bytes:574 acl:0 sco:0 events:30 errors:0
TX bytes:368 acl:0 sco:0 commands:30 errors:0在我的示例中,我们可以看到一个蓝牙接口。这就是我们将要使用蓝牙完成所有想要做的事情的方式。您会看到它的当前状态为关闭,这意味着它无法执行任何操作,因此要使用蓝牙,我们需要做的第一件事就是打开接口。
如果我们插入了Wi-Fi接口,但尚未启动,则可以输入ifconfig,然后输入接口名称,然后输入up。由于hciconfig与ifconfig基本相同,因此我们可以使用许多相同的命令,您可以在其手册页中看到它们。
~# man hciconfig
HCICONFIG(1) Linux System Administration HCICONFIG(1)
NAME
hciconfig - configure Bluetooth devices
SYNOPSIS
hciconfig -h
hciconfig [-a]
hciconfig [-a] hciX [command [command parameters]]
DESCRIPTION
hciconfig is used to configure Bluetooth devices. hciX is the name of
a Bluetooth device installed in the system. If hciX is not given, hci‐
config prints name and basic information about all the Bluetooth de‐
vices installed in the system. If hciX is given but no command is
given, it prints basic information on device hciX only. Basic informa‐
tion is interface type, BD address, ACL MTU, SCO MTU, flags (up, init,
running, raw, page scan enabled, inquiry scan enabled, inquiry, authen‐
tication enabled, encryption enabled).
OPTIONS
-h, --help
Gives a list of possible commands.
-a, --all
Other than the basic info, print features, packet type, link
policy, link mode, name, class, version.
COMMANDS
up Open and initialize HCI device.
down Close HCI device.
reset Reset HCI device.
rstat Reset statistic counters.
auth Enable authentication (sets device to security mode 3).
noauth Disable authentication.
encrypt Enable encryption (sets device to security mode 3).
noencrypt Disable encryption.
secmgr Enable security manager (current kernel support is limited).
nosecmgr Disable security manager.
piscan Enable page and inquiry scan.
noscan Disable page and inquiry scan.
iscan Enable inquiry scan, disable page scan.
pscan Enable page scan, disable inquiry scan.
ptype [type] With no type , displays the current packet types. Otherwise, all the packet types specified by type are set. type is a comma-separated list of packet types, where the possible packet types are DM1, DM3, DM5, DH1, DH3, DH5, HV1, HV2, HV3.
name [name] With no name, prints local name. Otherwise, sets local name to name.
class [class] With no class, prints class of device. Otherwise, sets class of device to class. class is a 24-bit hex number describing the class of device, as specified in section 1.2 of the Bluetooth Assigned Numers document.
voice [voice] With no voice, prints voice setting. Otherwise, sets voice setting to voice. voice is a 16-bit hex number describing the voice setting.
iac [iac] With no iac, prints the current IAC setting. Otherwise, sets the IAC to iac.
inqtpl [level] With no level, prints out the current inquiry transmit power level. Otherwise, sets inquiry transmit power level to level.
inqmode [mode] With no mode, prints out the current inquiry mode. Otherwise, sets inquiry mode to mode.
inqdata [data] With no name, prints out the current inquiry data. Otherwise, sets inquiry data to data.
inqtype [type] With no type, prints out the current inquiry scan type. Otherwise, sets inquiry scan type to type.
inqparams [win:int] With no win:int, prints inquiry scan window and interval. Otherwise, sets inquiry scan window to win slots and inquiry scan interval to int slots.
pageparms [win:int] With no win:int, prints page scan window and interval. Otherwise, sets page scan window to win slots and page scan interval to int slots.
pageto [to] With no to, prints page timeout. Otherwise, sets page timeout to .I to slots.
afhmode [mode] With no mode, prints out the current AFH mode. Otherwise, sets AFH mode to mode.
sspmode [mode] With no mode, prints out the current Simple Pairing mode. Otherwise, sets Simple Pairing mode to mode.
aclmtu mtu:pkt Sets ACL MTU to to mtu bytes and ACL buffer size to pkt packets.
scomtu mtu:pkt Sets SCO MTU to mtu bytes and SCO buffer size to pkt packets.
delkey <bdaddr> This command deletes the stored link key for bdaddr from the device.
oobdata Get local OOB data (invalidates previously read data).
commands Display supported commands.
features Display device features.
version Display version information.
revision Display revision information.
lm [mode] With no mode , prints link mode. MASTER or SLAVE mean, respectively, to ask to become master or to remain slave when a connection request comes in. The additional keyword ACCEPT means that baseband connections will be accepted even if there are no listening AF_BLUETOOTH sockets. mode is NONE or a comma-separated list of keywords, where possible keywords are MASTER and ACCEPT . NONE sets link policy to the default behaviour of remaining slave and not accepting baseband connections when there are no listening AF_BLUETOOTH sockets. If MASTER is present, the device will ask to become master if a connection request comes in. If ACCEPT is present, the device will accept baseband connections even when there are no listening AF_BLUETOOTH sockets.
AUTHORS
Written by Maxim Krasnyansky <maxk@qualcomm.com> and Marcel Holtmann <marcel@holtmann.org>
man page by Fabrizio Gennari <fabrizio.gennari@philips.com>
BlueZ Nov 11 2002 HCICONFIG(1)
Manual page hciconfig(1) line 147/169 (END) (press h for help or q to quit)我们可以在手册页中看到这是用于配置蓝牙设备的,因此,如果您有该外部蓝牙设备或插入的东西,也可以使用它来查看已连接的设备并对其进行适当的配置。
现在,我们对hciconfig有了更多了解,让我们继续并按Q退出。我们需要拿起发现的蓝牙设备并将其启动。只需输入hciconfig,然后输入我们找到的设备的名称,然后输入up。
~# hciconfig hci0 up要查看是否有效,请再次运行hciconfig命令:
~# hciconfig
hci0 Type: Primary Bus: USB
BD Address: ██:██:██:██:██:██ ACL MTU: 1022:8 SCO MTU: 183.5
UP RUNNING
RX bytes:1148 acl:0 sco:0 events:60 errors:0
TX bytes:736 acl:0 sco:0 commands:60 errors:0步骤2使用hcitool扫描蓝牙设备
现在,让我们使用hcitool查找正在发送发现信标的蓝牙设备(处于发现模式)。首先,让我们查看其手册页:
~# man hciconfig
HCITOOL(1) Linux System Administration HCITOOL(1)
NAME
hcitool - configure Bluetooth connections
SYNOPSIS
hcitool [-h]
hcitool [-i <hciX>] [command [command parameters]]
DESCRIPTION
hcitool is used to configure Bluetooth connections and send some spe‐
cial command to Bluetooth devices. If no command is given, or if the
option -h is used, hcitool prints some usage information and exits.
OPTIONS
-h Gives a list of possible commands
-i <hciX>
The command is applied to device hciX , which must be the name
of an installed Bluetooth device. If not specified, the command
will be sent to the first available Bluetooth device.
COMMANDS
dev Display local devices
inq Inquire remote devices. For each discovered device, Bluetooth device address, clock offset and class are printed.
scan Inquire remote devices. For each discovered device, device name are printed.
name <bdaddr> Print device name of remote device with Bluetooth address bdaddr.
info <bdaddr> Print device name, version and supported features of remote device with Bluetooth address bdaddr.
spinq Start periodic inquiry process. No inquiry results are printed.
epinq Exit periodic inquiry process.
cmd <ogf> <ocf> [parameters]
Submit an arbitrary HCI command to local device. ogf, ocf and parameters are hexadecimal bytes.
con Display active baseband connections
cc [--role=m|s] [--pkt-type=<ptype>] <bdaddr>
Create baseband connection to remote device with Bluetooth address bdaddr. Option --pkt-type specifies a list of allowed packet types. <ptype> is a comma-separated list of packet types, where the possible packet types are DM1, DM3, DM5, DH1, DH3, DH5, HV1, HV2, HV3. Default is to allow all packet types. Option --role can have value m (do not allow role switch, stay master) or s (allow role switch, become slave if the peer asks to become master). Default is m.
dc <bdaddr> [reason]
Delete baseband connection from remote device with Bluetooth address bdaddr. The reason can be one of the Bluetooth HCI error codes. Default is 19 for user ended connections. The value must be given in decimal.
sr <bdaddr> <role> Switch role for the baseband connection from the remote device to master or slave.
cpt <bdaddr> <packet types>
Change packet types for baseband connection to device with Bluetooth address bdaddr. packet types is a comma-separated list of packet types, where the possible packet types are DM1, DM3, DM5, DH1, DH3, DH5, HV1, HV2, HV3.
rssi <bdaddr> Display received signal strength information for the connection to the device with Bluetooth address bdaddr.
lq <bdaddr> Display link quality for the connection to the device with Bluetooth address bdaddr.
tpl <bdaddr> [type] Display transmit power level for the connection to the device with Bluetooth address bdaddr. The type can be 0 for the current transmit power level (which is default) or 1 for the maximum transmit power level.
afh <bdaddr> Display AFH channel map for the connection to the device with Bluetooth address bdaddr.
lp <bdaddr> [value] With no value, displays link policy settings for the connection to the device with Bluetooth address bdaddr. If value is given, sets the link policy settings for that connection to value. Possible values are RSWITCH, HOLD, SNIFF and PARK.
lst <bdaddr> [value] With no value, displays link supervision timeout for the connection to the device with Bluetooth address bdaddr. If value is given, sets the link supervision timeout for that connection to value slots, or to infinite if value is 0.
auth <bdaddr> Request authentication for the device with Bluetooth address bdaddr.
enc <bdaddr> [encrypt enable]
Enable or disable the encryption for the device with Bluetooth address bdaddr.
key <bdaddr> Change the connection link key for the device with Bluetooth address bdaddr.
clkoff <bdaddr> Read the clock offset for the device with Bluetooth address bdaddr.
clock [bdaddr] [which clock]
Read the clock for the device with Bluetooth address bdaddr. The clock can be 0 for the local clock or 1 for the piconet clock (which is default).
lescan [--privacy] [--passive] [--whitelist] [--discovery=g|l] [--duplicates]
Start LE scan
leinfo [--static] [--random] <bdaddr>
Get LE remote information
lewladd [--random] <bdaddr>
Add device to LE White List
lewlrm <bdaddr> Remove device from LE White List
lewlsz Read size of LE White List
lewlclr Clear LE White List
lerladd [--local irk] [--peer irk] [--random] <bdaddr>
Add device to LE Resolving List
lerlrm <bdaddr> Remove device from LE Resolving List
lerlclr Clear LE Resolving List
lerlsz Read size of LE Resolving List
lerlon Enable LE Address Resolution
lerloff Disable LE Address Resolution
lecc [--static] [--random] <bdaddr> | [--whitelist]
Create a LE Connection
ledc <handle> [reason]
Disconnect a LE Connection
lecup <handle> <min> <max> <latency> <timeout>
LE Connection Update
AUTHORS
Written by Maxim Krasnyansky <maxk@qualcomm.com> and Marcel Holtmann <marcel@holtmann.org>
man page by Fabrizio Gennari <fabrizio.gennari@philips.com>
BlueZ Nov 12 2002 HCITOOL(1)
Manual page hcitool(1) line 154/176 (END) (press h for help or q to quit)Hcitool用于配置和执行各种任务,例如扫描,查询和提取名称。这对于了解设备非常有用,但是其中一些命令需要使用MAC地址才能使用。
让我们看看其中一些命令。首先,我们将进行扫描。它将使用蓝牙接口扫描附近的蓝牙设备,并提供其MAC地址供我们进行其他扫描,查询或尝试获取设备名称。
~# hcitool scan
Scanning ...
00:1D:A5:00:09:1D OBDII在上方,我们看到了连接到车辆的OBD2连接器。那很有趣。使用MAC地址,我们现在可以执行另一个命令,该命令要求我们首先具有MAC地址。让我们尝试获取设备的名称:
~# hcitool name 00:1D:A5:00:09:1D
OBDII那应该可以让我们获取设备的名称,但是从第一次扫描中我们就知道了。但是,如果我们不知道它,它将使我们能够了解更多有关它的信息。要了解更多信息,我们可以使用inq命令:
~# hcitool inq 00:1D:A5:00:09:1D
Scanning ...
00:1D:A5:00:09:1D clock offset: 0x21c0 class: ox5a020c请注意,它还会显示时钟偏移量和类别。该类指示它是哪种蓝牙设备,我们可以通过转到蓝牙站点来查找代码。或者,正如我们稍后将看到的,一些工具可以为我们完成它。
步骤3使用sdptool扫描服务
要了解有关服务的更多信息,我们可以使用一个名为sdptool的工具来浏览有关设备上可用内容的更多信息,并了解属性-也许我们可以做或不能做的事情。我们将需要再次使用MAC地址,但首先,让我们也检查一下其手册页:
~# man sdptool
sdptool(1) General Commands Manual sdptool(1)
NAME
sdptool — control and interrogate SDP servers
SYNOPSIS
sdptool [options] {command} [command parameters ...]
DESCRIPTION
sdptool provides the interface for performing SDP queries on Bluetooth
devices, and administering a local SDP database.
COMMANDS
The following commands are available. In all cases bdaddr specifies
the device to search or browse. If local is used for bdaddr, then the
local SDP database is searched.
Services are identified and manipulated with a 4-byte record_handle
(NOT the service name). To find a service's record_handle, look for
the "Service RecHandle" line in the search or browse results
search [--bdaddr bdaddr] [--tree] [--raw] [--xml] service_name
Search for services.. Known service names are DID, SP, DUN, LAN, FAX, OPUSH, FTP, HS, HF, HFAG, SAP, NAP, GN, PANU, HCRP, HID, CIP, A2SRC, A2SNK, AVRCT, AVRTG, UDIUE, UDITE and SYNCML.
browse [--tree] [--raw] [--xml] [bdaddr]
Browse all available services on the device specified by a Bluetooth address as a parameter.
records [--tree] [--raw] [--xml] bdaddr
Retrieve all possible service records.
add [ --handle=N --channel=N ]
Add a service to the local SDP database. You can specify a handle for this record using the --handle option. You can specify a channel to add the service on using the --channel option. NOTE: Local adapters configuration will not be updated and this command should be used only for SDP testing.
del record_handle
Remove a service from the local SDP database. NOTE: Local adapters configuration will not be updated and this command should be used only for SDP testing.
get [--tree] [--raw] [--xml] [--bdaddr bdaddr] record_handle
Retrieve a service from the local SDP database.
setattr record_handle attrib_id attrib_value
Set or add an attribute to an SDP record.
setseq record_handle attrib_id attrib_values
Set or add an attribute sequence to an SDP record.
OPTIONS
--help Displays help on using sdptool.
EXAMPLES
sdptool browse 00:80:98:24:15:6D
sdptool browse local
sdptool add DUN
sdptool del 0x10000
BUGS
Documentation needs improving.
AUTHOR
Maxim Krasnyansky <maxk@qualcomm.com>. Man page written by Edd Dumbill <ejad@debian.org>.
sdptool(1)
Manual page sdptool(1) line 60/82 (END) (press h for help or q to quit)它使我们能够配置,控制和询问SDP(服务发现协议)服务器。因此,它使我们能够在蓝牙设备上进行查询,并精确找出权限发生了什么以及我们可能会开始使用那些服务。
退出手册页,然后键入sdptool,然后浏览,然后输入捕获的MAC地址。
~# sdptool browse 00:1D:A5:00:09:1D
Browsing 00:1D:A5:00:09:1D ...
Service Name: SPP
Service RecHandle: 0x10001
Service Class ID List:
"Serial Port" (ox1101)
Protocol Descriptor List:
"L2CAP" (0x0100)
"RFCOMM" (0x0003)
Channel: 1在这里,我们可以看到有关通信,协议的更多信息,也许我们甚至可以开始发现设备中是否存在漏洞,或者我们是否能够直接与之通信。我们甚至可以找到它是使用MAC地址随机化还是类似的方式。
步骤4使用l2ping ping蓝牙设备
现在我们有了附近所有设备的MAC地址,我们可以使用称为l2ping的工具ping它们,无论它们是否处于发现模式,以查看它们是否可以到达。对我来说,这只是一台设备。在这样做之前,让我们运行该工具的手册页,以查看所有可用内容。
~# man l2ping
L2PING(1) Linux System Administration L2PING(1)
NAME
l2ping - Send L2CAP echo request and receive answer
SYNOPSIS
l2ping [-i <hciX>] [-s size] [-c count] [-t timeout] [-d delay] [-f]
[-r] [-v] bd_addr
DESCRIPTION
L2ping sends a L2CAP echo request to the Bluetooth MAC address bd_addr
given in dotted hex notation.
OPTIONS
-i <hciX> The command is applied to device hciX , which must be the name of an installed Bluetooth device (X = 0, 1, 2, ...) If not specified, the command will be sent to the first available Bluetooth device.
-s size The size of the data packets to be sent.
-c count Send count number of packets then exit.
-t timeout Wait timeout seconds for the response.
-d delay Wait delay seconds between pings.
-f Kind of flood ping. Use with care! It reduces the delay time between packets to 0.
-r Reverse ping (gnip?). Send echo response instead of echo request.
-v Verify response payload is identical to request payload. It is not required for remote stacks to return the request payload, but most stacks do (including Bluez).
bd_addr The Bluetooth MAC address to be pinged in dotted hex notation like 01:02:03:ab:cd:ef or 01:EF:cd:aB:02:03
AUTHORS
Written by Maxim Krasnyansky <maxk@qualcomm.com> and Marcel Holtmann <marcel@holtmann.org>
man page by Nils Faerber <nils@kernelconcepts.de>, Adam Laurie <adam@algroup.co.uk>.
BlueZ Jan 22 2002 L2PING(1)
Manual page l2ping(1) line 32/54 (END) (press h for help or q to quit)我们不需要在这里做任何花哨的操作,只需对蓝牙设备执行以下操作:
~# l2ping 00:1D:A5:00:09:1D
Ping: 00:1D:A5:00:09:1D from ██:██:██:██:██:██ (data size 44) ...
44 bytes from 00:1D:A5:00:09:1D id 0 time 37.57ms
44 bytes from 00:1D:A5:00:09:1D id 1 time 27.23ms
44 bytes from 00:1D:A5:00:09:1D id 2 time 27.59ms
44 bytes from 00:1D:A5:00:09:1D id 3 time 27.31ms
44 bytes from 00:1D:A5:00:09:1D id 4 time 40.99ms
44 bytes from 00:1D:A5:00:09:1D id 5 time 48.77ms
44 bytes from 00:1D:A5:00:09:1D id 6 time 59.93ms
44 bytes from 00:1D:A5:00:09:1D id 7 time 48.84ms
44 bytes from 00:1D:A5:00:09:1D id 8 time 67.59ms这表明设备在范围内并且可以访问。
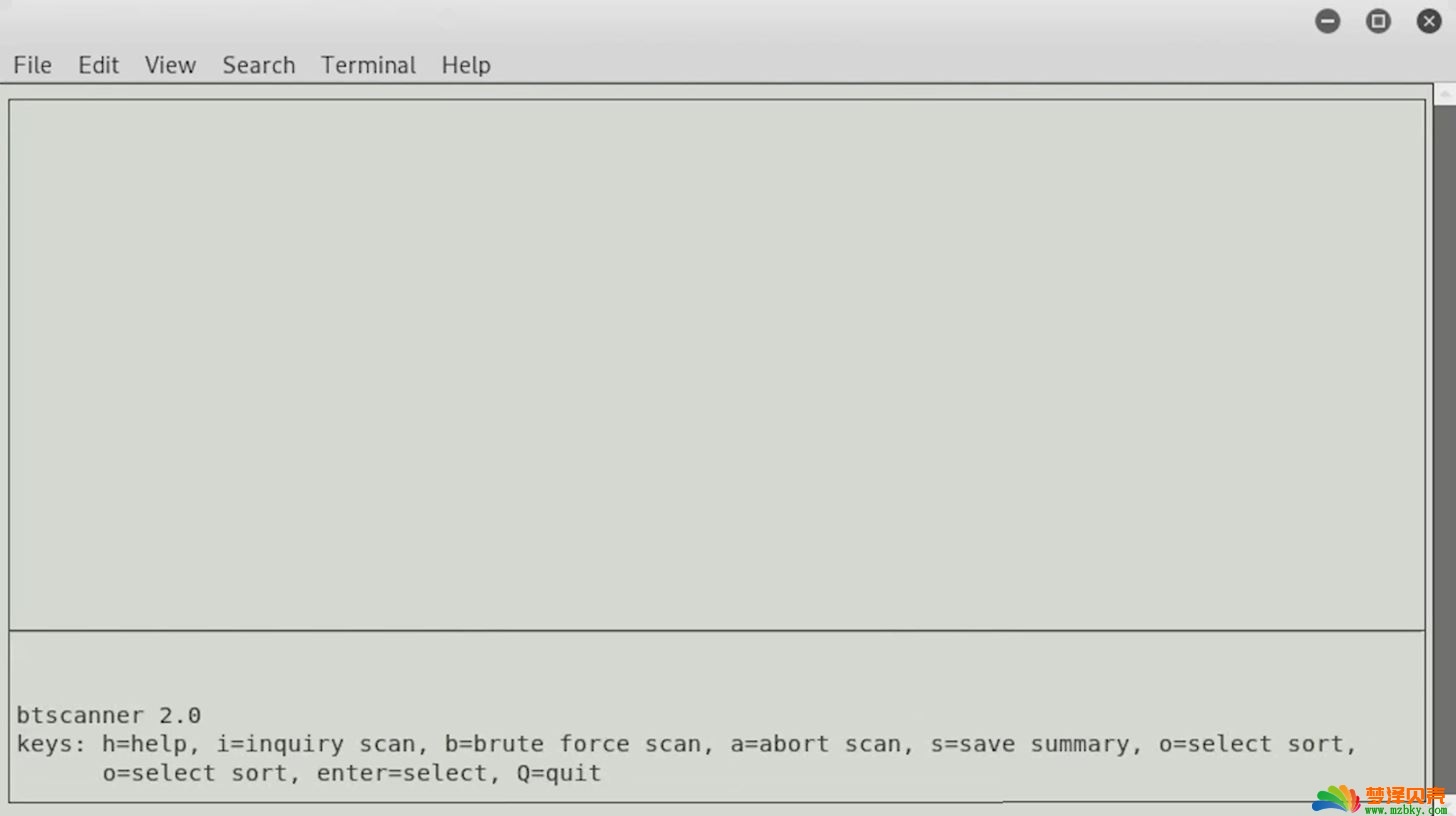
步骤5使用btscanner扫描蓝牙设备
现在是时候继续介绍我们要介绍的最后一个工具,它是一个用于发现蓝牙设备的全功能图形用户界面。它称为btscanner,一旦启动它,我们可以输入btscanner。但是在进行此操作之前,由于我们已经查看了其余工具的手册页,因此我们也快速浏览一下:
~# man btscanner
BTSCANNER(1) General Commands Manual BTSCANNER(1)
NAME
btscanner - ncurses-based scanner for Bluetooth devices
SYNOPSIS
btscanner [--help] [--cfg <file>] [--no-reset]
DESCRIPTION
This manual page was written for the Debian GNU/Linux distribution be‐
cause the original program does not have a manual page.
btscanner is a tool designed specifically to extract as much informa‐
tion as possible from a Bluetooth device without the requirement to
pair. A detailed information screen extracts HCI and SDP information,
and maintains an open connection to monitor the RSSI and link quality.
btscanner is based on the BlueZ Bluetooth stack, which is included with
recent Linux kernels, and the BlueZ toolset. btscanner also contains a
complete listing of the IEEE OUI numbers and class lookup tables. Using
the information gathered from these sources it is possible to make edu‐
cated guesses as to the host device type.
OPTIONS
--help Show a help text and exit.
--cfg <file> Use <file> as the config file.
--no-reset Do not reset the Bluetooth adapter before scanning.
BUGS
Please report any bugs to Tim Hurman <tim.hurman@pentest.co.uk>.
LICENCE
btscanner is covered by the GNU General Public License (GPL).
SEE ALSO
kismet(1).
AUTHORS
Tim Hurman <tim.hurman@pentest.co.uk>
This manual page was written by Uwe Hermann <uwe@hermann-uwe.de>, for
the Debian GNU/Linux system (but may be used by others).
April 22, 2006 BTSCANNER(1)
Manual page btscanner(1) line 23/45 (END) (press h for help or q to quit)您可以看到btscanner没什么要紧的,那是因为它是一个GUI工具,所以所有的魔术都在运行该工具后发生,所以现在就开始做吧:
~# btscanner
Opening the OUI database
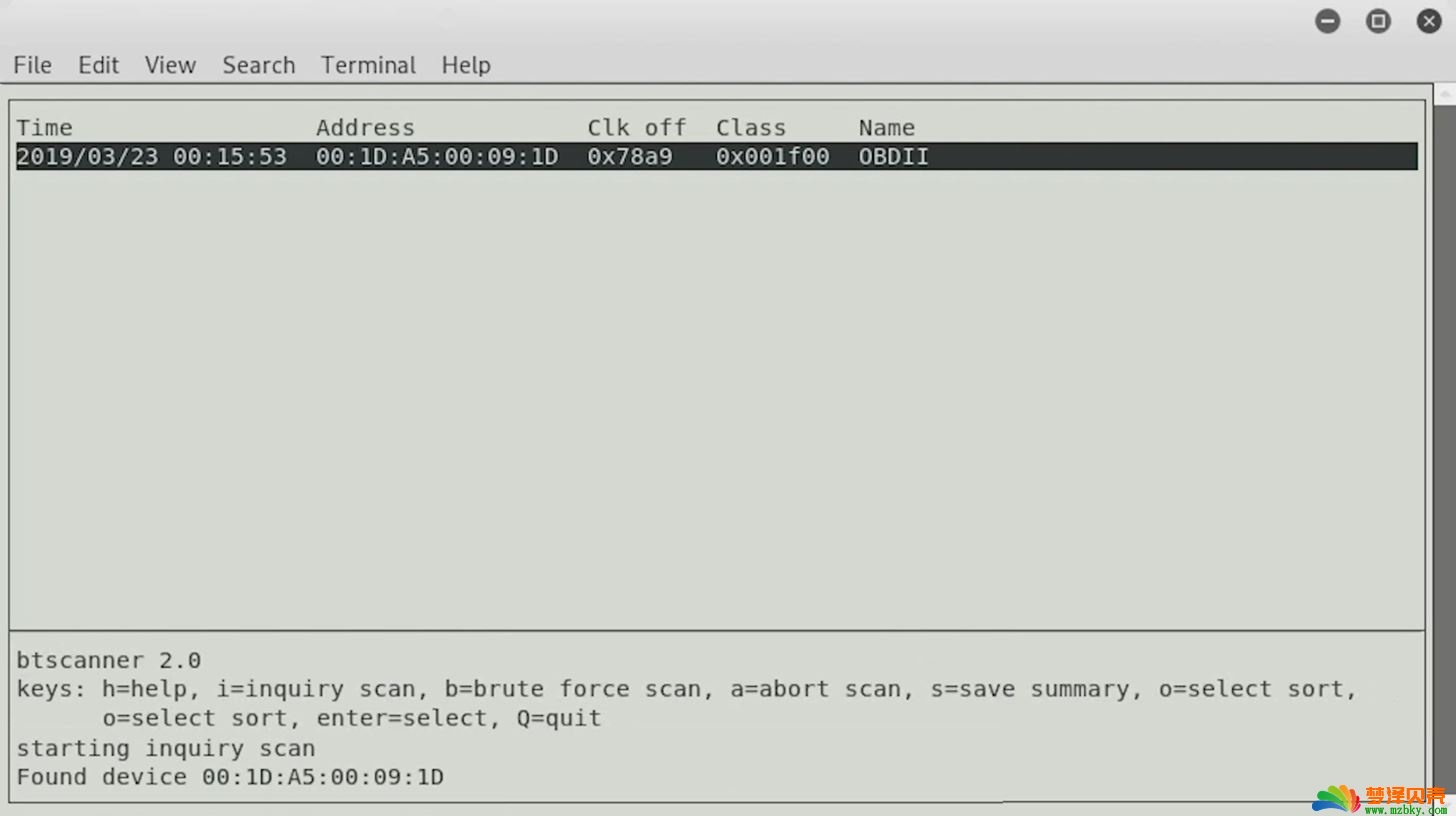
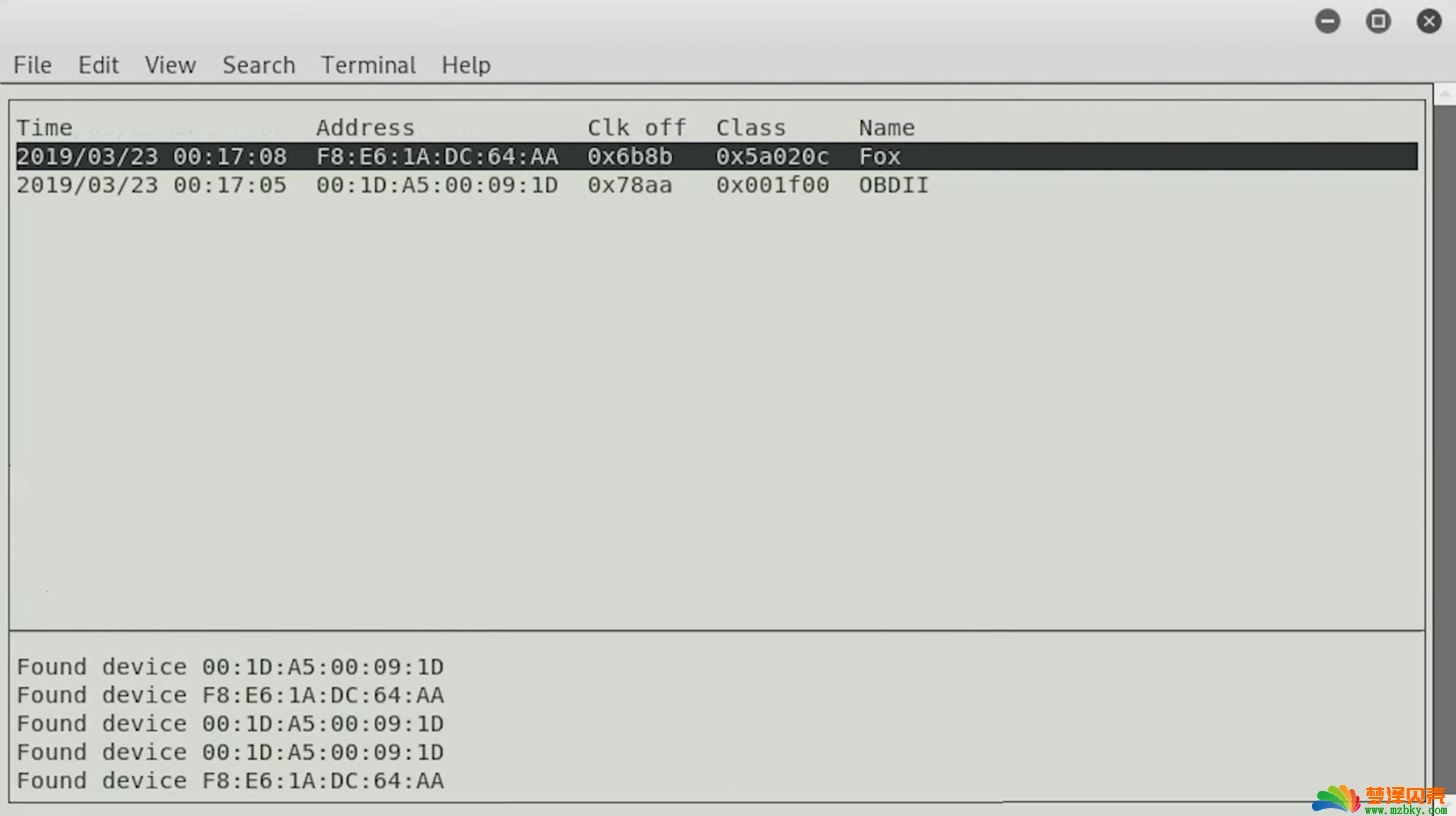
Reading the OUT database该界面可能看起来类似于熟悉Kismet界面的人员,这种界面使我们能够以GUI的感觉以命令行格式进行很多工作。这是有益而又酷的,因为这意味着通过输入i,我们可以开始进行查询扫描并找到附近的Bluetooth设备,并且它可以允许我们连接或设置命令或类似的命令。
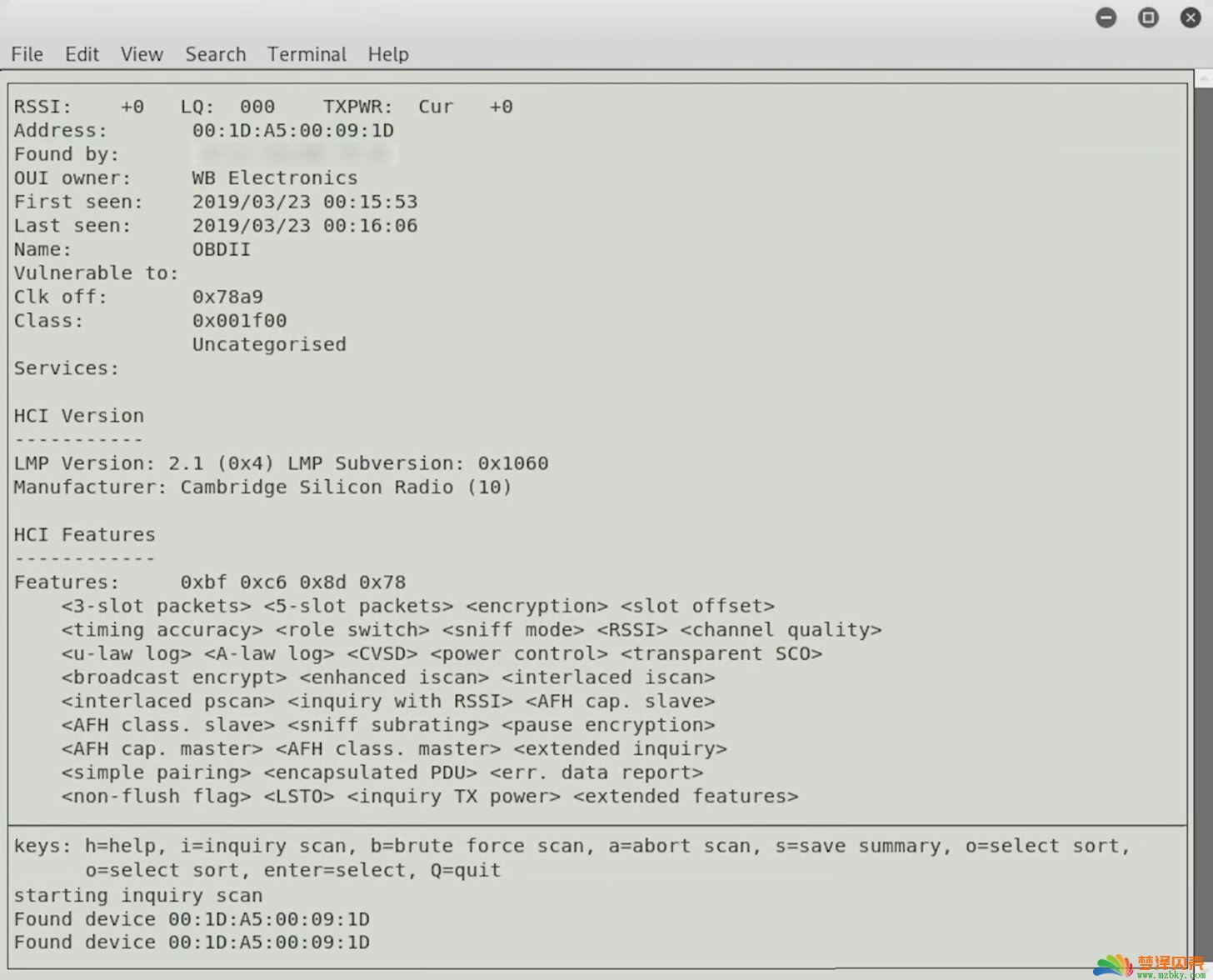
我们找到了一个设备,它与以前看到的是相同的蓝牙设备,并且我相信我们可以在其他设备滚动时找到它们。现在,我们可以继续并按Enter键以了解有关设备。
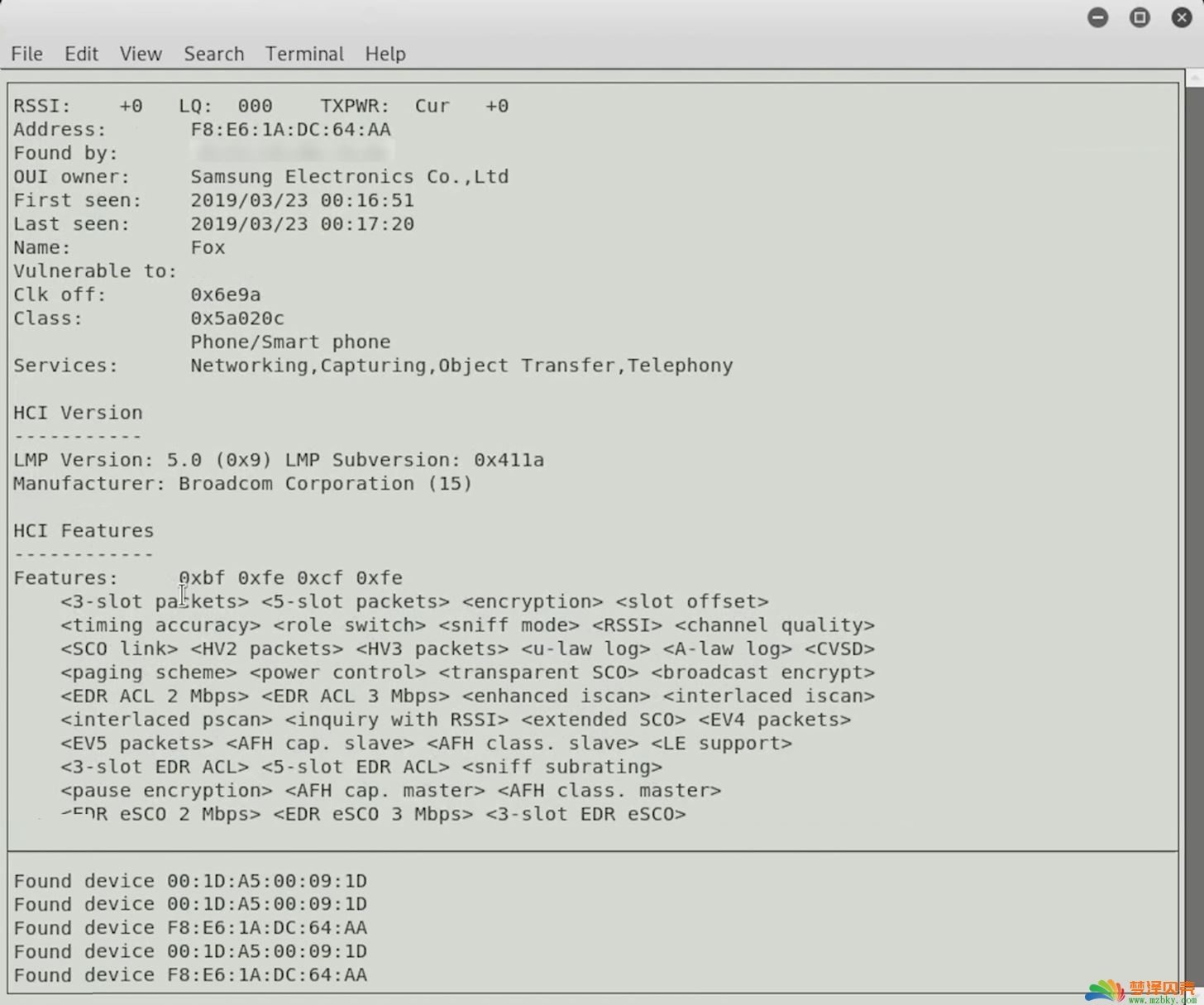
在这里,我们可以看到设备的名称,所有者,这很有趣,然后可以看到有关正在宣传的各种功能的更多信息。
要返回主窗口,请按Q,然后在发现其他设备或它们进入范围内时,我们可以在此处找到它们,并开始更多地了解这些设备在做什么,它们正在与哪些设备进行通信以及它们在做什么。他们有能力,还有更多。
如果您的计算机上没有蓝牙,则可以始终插入蓝牙适配器,但是在继续进行故障排除之前,可能需要检查以确保其兼容。我不确定每个蓝牙适配器是否都可以与每个Linux程序一起使用。
在上方,您可以看到我们找到了第二个设备,所以让我们继续单击它。
我们可以看到这是一部智能手机-三星设备-它比起第一台设备具有更多的功能和我们可以做的事情。我们已经能够伸手并开始寻找不同的设备。我们可以开始了解它们,也许是运行在它们后面的软件,当然还可以查看他们正在宣传的服务,以了解它是否代表了良好的攻击面。
以上所有操作都是使用Kali Linux的完全更新版本完成的,我们无需安装任何东西。因此,如果您从Kali Linux重新开始学习,这是使用一些内置工具来接触并触摸您周围的蓝牙设备的好方法,并且可以开始了解这些多功能强大工具中的每一个功能的。
到目前为止我们学到了什么
今天,我们探索了蓝牙侦察,并且可以使用此信息做一些更高级的事情。许多蓝牙设备都不会随意将其MAC地址随机化,这意味着它始终都是一样的。可以用来追踪一个地方的人。
例如,Tile蓝牙跟踪器,您可以在其中运行任何应用程序的人找到丢失的物品。这意味着一个人是可追踪的,没有办法将其关闭。如果您想退出这种跟踪,请确保在手机等设备上禁用蓝牙。但是对于自然打开的设备(例如Tile跟踪器),除了将其留在家里之外别无选择。
本站原创文章,作者:小 编,如若转载,请注明出处:https://www.mzbky.com/1376.html
 微信扫一扫
微信扫一扫  支付宝扫一扫
支付宝扫一扫